EDR: Why 75% of US Cybersecurity Experts Recommend It for 2026

Anúncios
Endpoint Detection and Response (EDR) is poised to be a cornerstone of cybersecurity strategies, with 75% of US cybersecurity experts advocating for its adoption by 2026 due to its unparalleled ability to proactively detect and neutralize advanced threats across all digital endpoints.
Anúncios
In the rapidly evolving landscape of cyber threats, organizations constantly seek robust defenses. By 2026, a staggering 75% of US cybersecurity experts recommend adopting Endpoint Detection and Response (EDR) solutions, signaling a critical shift in how enterprises approach digital security. This widespread endorsement highlights EDR’s effectiveness in combating sophisticated attacks that bypass traditional security measures.
The evolving threat landscape and EDR’s emergence
The digital world faces an unprecedented surge in cyberattacks, from ransomware and phishing to advanced persistent threats (APTs). Traditional antivirus software, while still necessary, often falls short against polymorphic malware and fileless attacks. This growing complexity has necessitated a more dynamic and intelligent security paradigm.
Anúncios
EDR systems emerged as a direct response to these evolving challenges. Unlike static security tools, EDR continuously monitors endpoints—such as laptops, servers, and mobile devices—for suspicious activities, providing real-time visibility and advanced threat detection capabilities. This proactive stance is crucial in an environment where a single compromised endpoint can jeopardize an entire network.
Beyond signature-based detection
One of EDR’s primary advantages is its move beyond traditional signature-based detection. While signatures can identify known threats, they are ineffective against zero-day exploits and novel attack vectors. EDR leverages behavioral analytics, machine learning, and artificial intelligence to identify anomalies and malicious patterns that may indicate a sophisticated attack.
- Behavioral analysis: Monitors user and system behavior for deviations from the norm.
- Machine learning: Continuously learns from new threat data to improve detection accuracy.
- Threat intelligence integration: Correlates internal data with global threat feeds for broader context.
- Heuristic analysis: Identifies potential threats based on known malicious characteristics, even without a specific signature.
The ability to detect and analyze threats in real-time, coupled with automated response capabilities, positions EDR as an indispensable tool for modern cybersecurity. It transforms an organization’s defense from reactive to proactive, significantly reducing the window of opportunity for attackers.
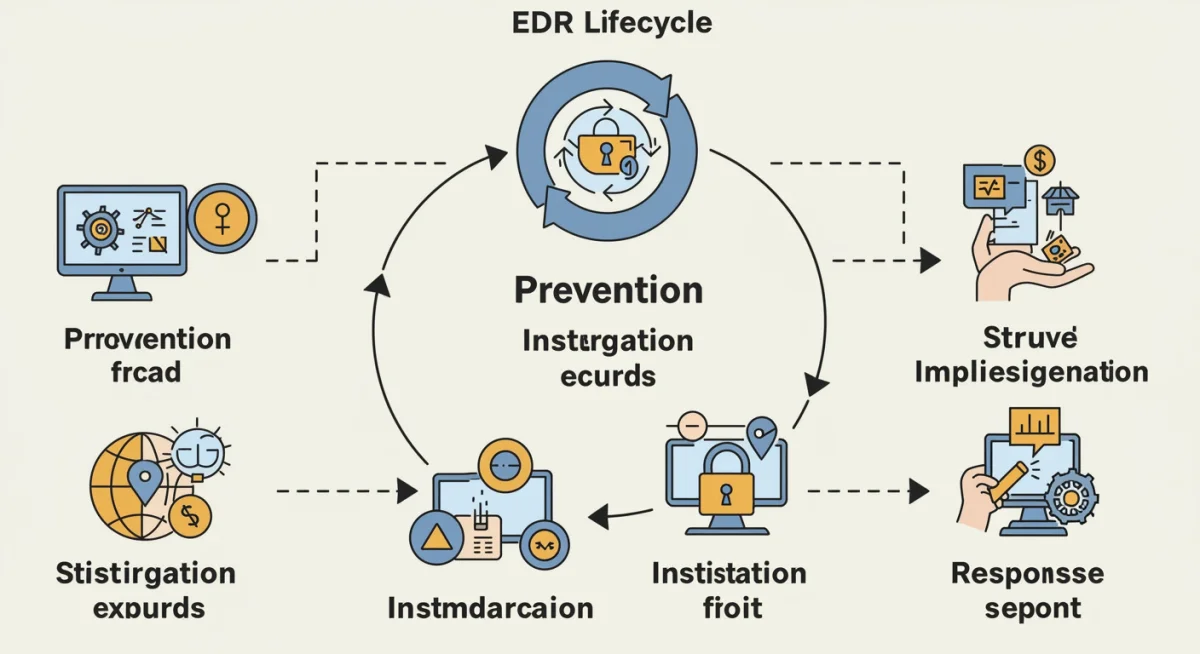
Core functionalities of EDR solutions
EDR solutions are designed to provide a holistic view of endpoint security, offering a suite of functionalities that span detection, investigation, and response. These core capabilities are what make EDR so highly recommended by experts for navigating the complex threat landscape of 2026.
At its heart, EDR is about visibility and control. It collects vast amounts of data from endpoints, including process execution, network connections, file system changes, and user activity. This data is then analyzed to identify potential threats that might otherwise go unnoticed by conventional security tools.
Comprehensive data collection and analysis
The foundation of any effective EDR system lies in its ability to collect comprehensive data from every endpoint. This continuous stream of information allows security teams to reconstruct attack sequences, understand their scope, and identify the root cause of a breach.
- Endpoint monitoring: Constant surveillance of all endpoint activities.
- Data aggregation: Centralized collection of telemetry data from diverse sources.
- Contextualization: Enriching raw data with threat intelligence and business context.
Through advanced analytics, EDR can correlate seemingly disparate events to uncover sophisticated attacks. For instance, an unusual login attempt followed by a rapid data transfer to an unknown external server might be flagged as highly suspicious, even if individual events appear benign.
Automated response and remediation
Beyond detection, EDR excels in its ability to automate responses to identified threats. This automation is crucial for minimizing damage, especially when human intervention might be too slow. EDR can isolate compromised endpoints, terminate malicious processes, and roll back system changes, effectively containing an attack before it escalates.
The automated response mechanisms in EDR are not just about speed; they also reduce the burden on security analysts, allowing them to focus on more complex investigations. This efficiency is a key factor in why experts foresee EDR as essential for cybersecurity resilience in the coming years.
Why 75% of US cybersecurity experts endorse EDR
The overwhelming consensus among US cybersecurity experts regarding EDR’s importance by 2026 stems from several critical factors. These factors highlight EDR’s unique ability to address the most pressing security challenges faced by organizations today.
Experts recognize that the nature of cyber threats has fundamentally changed. Attackers are more sophisticated, persistent, and capable of evading traditional defenses. EDR provides the necessary depth of visibility and automated response capabilities to counter these modern threats effectively.
Addressing advanced persistent threats (APTs)
APTs are particularly challenging because they often involve stealthy, long-term campaigns designed to infiltrate networks and exfiltrate sensitive data without detection. EDR’s continuous monitoring and behavioral analysis are crucial for identifying the subtle indicators of an APT.
By tracking granular activities across endpoints, EDR can spot the lateral movement, privilege escalation, and data staging that are hallmarks of APTs. This capability is a significant reason for its high recommendation.
Improved incident response capabilities
Effective incident response is paramount in limiting the impact of a breach. EDR streamlines this process by providing detailed forensic data and automated remediation actions. Security teams can quickly understand the scope of an attack, identify affected systems, and take decisive action.
This enhanced incident response capability translates into reduced downtime, minimized data loss, and ultimately, a stronger security posture. The ability to respond rapidly and effectively is a core benefit driving expert endorsement.
Compliance and regulatory requirements
In an era of stringent data protection regulations, organizations face increasing pressure to demonstrate robust security controls. EDR solutions help meet these compliance requirements by providing detailed audit trails, evidence of threat detection, and response activities.
Maintaining compliance with regulations like GDPR, CCPA, and HIPAA often necessitates the advanced logging and monitoring capabilities that EDR offers. This aspect makes EDR not just a security best practice, but also a regulatory necessity for many businesses.
Integrating EDR into your existing security architecture
Implementing an EDR solution is not about replacing existing security tools but rather enhancing them. Successful integration of EDR into an organization’s security architecture requires careful planning and consideration of how it will complement other layers of defense.
EDR acts as a force multiplier, providing deeper insights and more effective responses when combined with firewalls, intrusion detection systems, and security information and event management (SIEM) platforms. It fills critical gaps that these traditional tools might miss.
Synergy with SIEM and SOAR platforms
EDR data can significantly enrich a SIEM platform, providing granular endpoint telemetry that helps security analysts correlate events and identify complex attack patterns. This integration offers a more comprehensive view of an organization’s security posture.
Furthermore, EDR can feed directly into Security Orchestration, Automation, and Response (SOAR) platforms, enabling automated playbooks for incident response. This synergy allows for faster, more efficient handling of security alerts, reducing alert fatigue and improving overall operational efficiency.
- Enhanced visibility: EDR augments SIEM data with endpoint-specific insights.
- Automated workflows: SOAR platforms leverage EDR alerts for rapid response.
- Centralized management: Streamlined security operations through integrated platforms.
Seamless integration with network security tools
While EDR focuses on endpoints, its effectiveness is amplified when integrated with network security tools. For example, a network intrusion detection system might flag suspicious traffic, and EDR can then investigate the specific endpoint involved to determine the nature and scope of the threat.
This layered approach ensures that organizations have visibility and control at both the network and endpoint levels, creating a more resilient and adaptive defense against a wide array of cyber threats. Compatibility and API availability are key considerations during integration.
Challenges and considerations for EDR adoption
While the benefits of EDR are clear, organizations must also be aware of potential challenges and considerations when adopting these solutions. Addressing these proactively can ensure a smoother implementation and maximize the return on investment.
The complexity of EDR solutions, the volume of data they generate, and the need for skilled personnel are all factors that organizations must account for before deployment. Proper planning and resource allocation are essential for success.
Managing data volume and false positives
EDR systems generate a significant amount of data, which can be overwhelming for security teams. Without proper tools and processes, this data deluge can lead to alert fatigue and an increased number of false positives, potentially obscuring real threats.
Organizations need to invest in robust analytics capabilities and potentially leverage managed EDR services to effectively process and prioritize alerts. Tuning the EDR solution to reduce noise while maintaining detection accuracy is a continuous process.
Skill gaps and talent acquisition
Operating and optimizing an EDR solution requires specialized skills in threat hunting, incident response, and forensic analysis. Many organizations face a shortage of cybersecurity professionals with these specific competencies.
To overcome this, companies may need to invest in training existing staff, recruit new talent, or outsource EDR management to a third-party security provider. The human element remains crucial for leveraging EDR’s full potential.
Cost of implementation and maintenance
EDR solutions represent a significant investment, not only in terms of software licenses but also for infrastructure, training, and ongoing management. Organizations must conduct a thorough cost-benefit analysis to justify the expenditure.
However, the cost of a data breach—including regulatory fines, reputational damage, and business disruption—often far outweighs the investment in EDR. This makes EDR a necessary expense for maintaining business continuity and trust.
The future of EDR and cybersecurity in 2026
Looking ahead to 2026, EDR is expected to evolve further, becoming even more integrated and intelligent. The trend towards extended detection and response (XDR) is already gaining momentum, promising an even broader scope of threat visibility and response capabilities.
The future of cybersecurity will be defined by highly automated, AI-driven solutions that can anticipate and neutralize threats before they materialize. EDR is a foundational component of this future, continuously adapting to the ever-changing threat landscape.
Rise of XDR (Extended Detection and Response)
XDR builds upon EDR by integrating security data from a wider range of sources, including networks, cloud environments, email, and identity systems. This comprehensive approach provides a more unified view of an organization’s attack surface, enabling more effective threat hunting and incident response.
The transition from EDR to XDR represents a natural evolution, driven by the need for consolidated security operations and improved threat context. Experts anticipate XDR to become the preferred security architecture for many enterprises by 2026.
- Unified visibility: Correlates data across multiple security layers.
- Enhanced automation: Automates detection and response across the entire IT estate.
- Reduced complexity: Simplifies security management through a single platform.
AI and machine learning advancements
Artificial intelligence and machine learning will continue to play an increasingly critical role in EDR and XDR solutions. These technologies will enable more accurate threat detection, faster incident response, and predictive analytics to identify potential vulnerabilities before they are exploited.
The ability of AI to process vast amounts of data and identify subtle patterns that human analysts might miss will be indispensable in the fight against advanced cyber threats. This continuous innovation ensures that EDR remains at the forefront of digital defense.
| Key EDR Aspect | Brief Description |
|---|---|
| Advanced Threat Detection | Goes beyond signatures using behavioral analytics and AI to spot novel and sophisticated attacks. |
| Real-time Visibility | Provides continuous monitoring of all endpoint activities for immediate threat insights. |
| Automated Response | Quickly isolates compromised endpoints and remediates threats automatically to minimize damage. |
| Future Evolution (XDR) | Expanding EDR’s scope to integrate data from networks, cloud, and identity for unified security. |
Frequently asked questions about EDR in 2026
EDR surpasses traditional antivirus by utilizing behavioral analytics, machine learning, and continuous monitoring to detect unknown and sophisticated threats like zero-day attacks and APTs, which often evade signature-based detection. It provides deeper visibility and proactive response capabilities.
Implementing EDR offers benefits such as enhanced threat detection against advanced attacks, improved incident response times, comprehensive visibility into endpoint activities, and automated remediation capabilities, all contributing to a stronger overall security posture and compliance.
EDR integrates by feeding rich endpoint telemetry data to SIEM platforms, enriching event correlation and providing a more complete picture of security incidents. This collaboration allows for better threat intelligence and more informed decision-making within a unified security ecosystem.
Organizations may encounter challenges such as managing the high volume of data generated by EDR, dealing with potential false positives, addressing skill gaps in cybersecurity teams, and the initial cost of implementation and ongoing maintenance. Careful planning is essential for success.
The future of EDR involves increased AI and machine learning integration, and its evolution into Extended Detection and Response (XDR). XDR broadens EDR’s scope by correlating data from networks, cloud, email, and identity, offering a more unified and comprehensive security approach.
Conclusion
The resounding endorsement of EDR by 75% of US cybersecurity experts for 2026 underscores its indispensable role in modern digital defense. As cyber threats continue to grow in sophistication, EDR provides the critical capabilities needed to detect, investigate, and respond to attacks across all endpoints, moving beyond the limitations of traditional security measures. Its integration with existing security architectures, coupled with advancements in AI and the emergence of XDR, positions EDR as a cornerstone for future cybersecurity strategies. Organizations that embrace EDR will be better equipped to protect their digital assets, maintain compliance, and ensure business continuity in an increasingly hostile cyber landscape.





