EDR Solutions 2026: A Comprehensive Comparison for U.S. Businesses

Anúncios
EDR Solutions 2026: A Comprehensive Comparison for U.S. Businesses
Anúncios
In the rapidly evolving landscape of cybersecurity, safeguarding your organization’s endpoints is no longer just a best practice—it’s a critical imperative. As we look towards 2026, the sophistication and frequency of cyber threats continue to escalate, making robust Endpoint Detection and Response (EDR) solutions an indispensable component of any effective security strategy for U.S. businesses. This comprehensive guide delves into the world of EDR Solutions Comparison, providing an in-depth analysis to help you navigate the myriad options available and make an informed decision for your enterprise.
The digital perimeter of businesses has expanded dramatically, encompassing a diverse array of devices from traditional desktops and laptops to mobile devices, servers, cloud workloads, and IoT endpoints. Each of these represents a potential entry point for adversaries. Traditional antivirus software, while still necessary, is often insufficient to combat advanced persistent threats (APTs), zero-day exploits, and sophisticated malware that can bypass signature-based detection. This is where EDR solutions step in, offering advanced capabilities to detect, analyze, investigate, and respond to threats in real-time, providing a proactive and reactive defense mechanism that is crucial in today’s threat environment.
Anúncios
Choosing the right EDR solution is a significant undertaking, requiring careful consideration of various factors such as your organization’s size, industry, specific security needs, budget, and existing IT infrastructure. Our goal with this article is to empower U.S. businesses with the knowledge and insights needed to select an EDR platform that not only meets their current security demands but is also scalable and adaptable to future challenges. We will explore the core functionalities of EDR, highlight key trends for 2026, and provide a detailed EDR Solutions Comparison of leading vendors in the market, focusing on their strengths, weaknesses, and suitability for different business contexts.
Understanding Endpoint Detection and Response (EDR): The Foundation of Modern Security
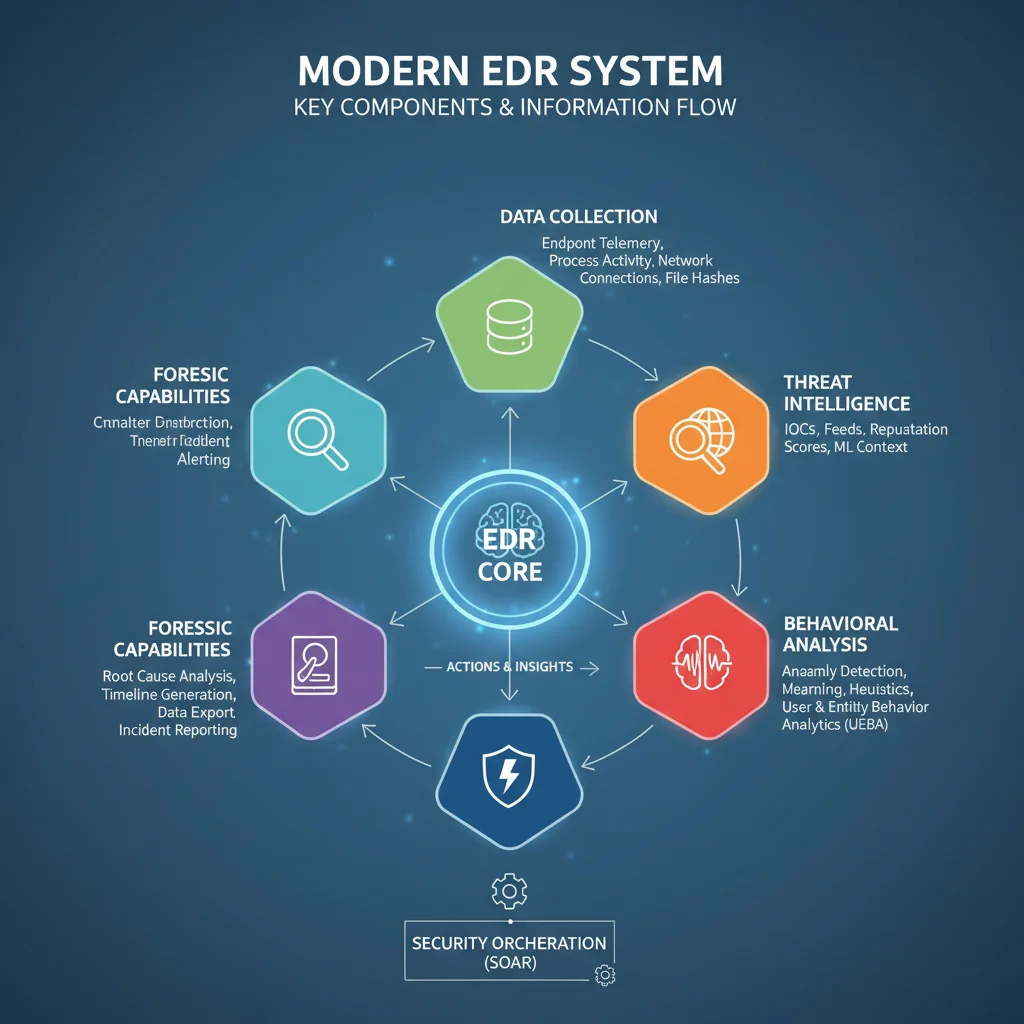
Before diving into a detailed EDR Solutions Comparison, it’s essential to grasp the fundamental principles and capabilities of EDR. At its core, EDR is a cybersecurity technology that continuously monitors endpoint devices for malicious activity and provides the tools to respond to and mitigate those threats. Unlike traditional antivirus, which primarily focuses on preventing known threats, EDR offers a more holistic and dynamic approach to endpoint security.
Key Capabilities of EDR Solutions:
- Continuous Monitoring and Data Collection: EDR solutions constantly collect vast amounts of data from endpoints, including process activity, file changes, network connections, user logins, and registry modifications. This rich telemetry is crucial for detecting subtle indicators of compromise (IoCs).
- Threat Detection and Analysis: Leveraging advanced analytics, machine learning (ML), artificial intelligence (AI), and behavioral analysis, EDR platforms identify suspicious activities and patterns that might indicate a cyberattack. This includes detecting anomalies, lateral movement, privilege escalation, and command-and-control communications.
- Automated and Manual Response: Upon detecting a threat, EDR provides various response capabilities. This can range from automated actions like isolating a compromised endpoint or terminating malicious processes, to providing security analysts with tools for manual investigation and remediation.
- Threat Hunting: EDR empowers security teams to proactively search for threats that might have bypassed automated defenses. By providing comprehensive visibility into endpoint activities and historical data, threat hunters can uncover hidden threats and zero-day attacks.
- Forensic Capabilities: In the event of a breach, EDR solutions offer detailed forensic data, allowing security professionals to understand the scope of the attack, how it occurred, and what data might have been compromised. This is vital for post-incident analysis and preventing future attacks.
- Integration with Security Ecosystems: Modern EDR platforms often integrate with other security tools like Security Information and Event Management (SIEM), Security Orchestration, Automation, and Response (SOAR), and vulnerability management systems to provide a unified security posture.
The evolution from basic antivirus to EDR reflects a shift in cybersecurity philosophy—from preventing known threats to detecting and responding to unknown and evolving threats. This proactive stance is what makes EDR a cornerstone of modern cybersecurity for U.S. businesses.
The Cybersecurity Landscape in 2026: What’s Driving EDR Adoption?
As we project to 2026, several key trends and challenges are shaping the cybersecurity landscape and reinforcing the critical need for advanced EDR Solutions Comparison and adoption:
1. Rise of Sophisticated Attacks:
Ransomware-as-a-Service (RaaS), supply chain attacks, and fileless malware continue to grow in complexity and evade traditional defenses. These attacks often leverage legitimate tools and processes, making them difficult to detect without behavioral analysis and deep visibility provided by EDR.
2. Expanding Attack Surface:
The proliferation of remote work, hybrid work models, cloud adoption, and the Internet of Things (IoT) has significantly expanded the attack surface for businesses. Endpoints are no longer confined to the corporate network, necessitating EDR solutions that can protect devices regardless of their location.
3. Regulatory Compliance:
U.S. businesses face stringent regulatory requirements such as HIPAA, PCI DSS, SOX, and various state-specific privacy laws. EDR solutions, with their robust logging, monitoring, and incident response capabilities, play a crucial role in demonstrating compliance and minimizing the impact of data breaches.
4. Shortage of Skilled Cybersecurity Professionals:
The ongoing shortage of cybersecurity talent means that businesses often struggle to staff their security operations centers (SOCs). EDR solutions, particularly those with strong automation and managed detection and response (MDR) services, can help bridge this gap by streamlining operations and augmenting existing teams.
5. Focus on Proactive Threat Hunting:
Organizations are moving beyond reactive defense to proactive threat hunting. EDR platforms provide the necessary data and tools for security analysts to actively seek out and neutralize threats before they can cause significant damage.
These trends underscore why a robust EDR strategy, backed by a carefully chosen solution, is paramount for U.S. businesses aiming to secure their digital assets in 2026.
Factors to Consider in an EDR Solutions Comparison for U.S. Businesses
Selecting the optimal EDR solution requires a thorough evaluation of various factors. This section outlines the critical aspects U.S. businesses should consider when conducting an EDR Solutions Comparison.
1. Detection Capabilities:
- Advanced Threat Detection: Does the EDR leverage AI/ML, behavioral analytics, and signatureless detection to identify zero-day exploits, fileless attacks, and advanced persistent threats?
- Threat Intelligence Integration: How well does it integrate with global and industry-specific threat intelligence feeds to enhance detection accuracy?
- MITRE ATT&CK Framework Alignment: Does the solution map detected activities to the MITRE ATT&CK framework, providing a standardized understanding of attacker tactics and techniques?
2. Response and Remediation:
- Automated Response: What automated response actions are available (e.g., process termination, file quarantine, network isolation)?
- Manual Remediation Tools: Does it provide granular control for security analysts to investigate and respond manually?
- Rollback Capabilities: Can the solution reverse malicious changes made to an endpoint?
3. Visibility and Analytics:
- Comprehensive Telemetry: What depth and breadth of endpoint data does it collect?
- Intuitive Dashboard and Reporting: Is the interface easy to navigate, and does it provide actionable insights and customizable reports?
- Historical Data Retention: How long is endpoint data retained for forensic analysis and threat hunting?
4. Performance and Scalability:
- Endpoint Performance Impact: How much overhead does the EDR agent impose on endpoint devices?
- Scalability: Can the solution easily scale to accommodate a growing number of endpoints and diverse operating systems?
- Cloud-Native Architecture: Is it a cloud-native solution, offering benefits like elastic scalability and reduced infrastructure management?
5. Ease of Use and Management:
- Deployment and Configuration: How straightforward is the initial deployment and ongoing configuration?
- Management Console: Is the management console user-friendly and efficient for security teams?
- Integration with Existing Tools: Does it integrate seamlessly with your existing security ecosystem (SIEM, SOAR, identity management)?
6. Support and Services:
- Vendor Support: What level of technical support is offered (24/7, dedicated account manager)?
- Managed Detection and Response (MDR): Does the vendor offer MDR services, which can be invaluable for organizations with limited in-house security resources?
- Training and Documentation: Are comprehensive training resources and documentation available?
7. Cost:
- Licensing Model: Is the pricing per endpoint, per user, or based on other metrics?
- Total Cost of Ownership (TCO): Consider not just licensing fees but also deployment, management, and potential integration costs.
Leading EDR Solutions Comparison for U.S. Businesses in 2026
Now, let’s delve into a detailed EDR Solutions Comparison of some of the leading vendors that U.S. businesses should consider in 2026. This comparison is not exhaustive but highlights prominent players and their distinct offerings.
1. CrowdStrike Falcon
- Strengths: Renowned for its cloud-native architecture, lightweight agent, and exceptional threat detection capabilities powered by AI and behavioral analytics. Strong focus on threat hunting and managed services (Falcon Complete). Excellent visibility and rapid response.
- Weaknesses: Can be perceived as premium-priced, and its advanced features might require specialized security talent to fully leverage without MDR services.
- Best For: Enterprises and mid-market companies seeking top-tier protection, advanced threat hunting, and those open to MDR services to augment their security teams.
2. SentinelOne Singularity
- Strengths: Offers robust AI-driven prevention, detection, and autonomous response capabilities. Known for its strong ransomware rollback features and ability to operate offline. Unified platform for EPP, EDR, and XDR.
- Weaknesses: Some users report a steeper learning curve for advanced configurations compared to others.
- Best For: Organizations prioritizing autonomous threat remediation, ransomware protection, and a unified security platform across various endpoints and cloud workloads.
3. Microsoft Defender for Endpoint
- Strengths: Deep integration with the broader Microsoft 365 ecosystem, offering seamless protection across Windows, macOS, Linux, and mobile devices. Strong detection capabilities, vulnerability management, and automated investigation and remediation. Often a cost-effective choice for existing Microsoft customers.
- Weaknesses: While strong on Microsoft platforms, multi-platform capabilities are continually improving but may not always match best-of-breed for non-Windows environments.
- Best For: Businesses heavily invested in the Microsoft ecosystem, looking for integrated security solutions and streamlined management.
4. Palo Alto Networks Cortex XDR
- Strengths: A comprehensive extended detection and response (XDR) platform that unifies EDR, network, cloud, and identity data for superior visibility and correlation. Strong emphasis on AI-driven analytics, threat intelligence, and automation.
- Weaknesses: Can be complex to deploy and manage for smaller organizations without dedicated security staff. Higher price point reflecting its XDR capabilities.
- Best For: Large enterprises and organizations that require a unified security operations platform beyond just endpoints, leveraging extensive data correlation.
5. Sophos Intercept X with EDR
- Strengths: Combines strong endpoint protection (EPP) with EDR capabilities, including deep learning AI and anti-ransomware technology (CryptoGuard). Known for its user-friendly interface and strong managed threat response (MTR) service.
- Weaknesses: While robust, its advanced threat hunting capabilities might not be as deep as some pure-play EDR vendors.
- Best For: Small to medium-sized businesses (SMBs) and mid-market companies looking for an integrated, easy-to-manage solution with strong protection and optional MDR services.
6. Carbon Black Cloud (VMware)
- Strengths: Offers robust behavioral analytics, threat hunting, and incident response capabilities. Strong focus on workload protection and integration with VMware’s virtualization ecosystem.
- Weaknesses: Some users report agent performance issues in certain environments, and the learning curve can be steep for new users.
- Best For: Organizations with significant VMware infrastructure, seeking advanced threat hunting and strong forensic capabilities.
This EDR Solutions Comparison provides a snapshot, but each vendor continuously innovates. It’s crucial for businesses to conduct their own proof-of-concept (POC) trials and engage with vendors directly to assess the best fit.
Emerging Trends and Future of EDR in 2026
The EDR landscape is dynamic, and several emerging trends will shape its evolution towards 2026, influencing future EDR Solutions Comparison efforts:
1. XDR (Extended Detection and Response) Dominance:
The push towards XDR will intensify. Businesses will increasingly seek platforms that unify security data from endpoints, networks, cloud, email, and identity to provide a more comprehensive view of threats and enable faster, more accurate detection and response. This convergence aims to break down security silos.
2. AI and Machine Learning Evolution:
AI and ML will become even more sophisticated, moving beyond anomaly detection to predictive analytics and autonomous remediation. This will enable EDR systems to anticipate attacks, understand attacker intent, and take pre-emptive actions with greater precision.
3. Cloud-Native and Serverless EDR:
As more workloads shift to the cloud, EDR solutions will continue their evolution towards fully cloud-native and serverless architectures, offering greater scalability, flexibility, and reduced operational overhead. This is particularly relevant for securing dynamic cloud environments.
4. Identity-Centric Security:
Identity will become a more central pillar of EDR. Solutions will increasingly integrate with identity and access management (IAM) systems to detect and respond to identity-based attacks, such as compromised credentials and privilege escalation, which are common attack vectors.
5. Automated Patching and Vulnerability Management Integration:
Closer integration between EDR and vulnerability management/patching solutions will become standard. This will allow EDR to not only detect threats but also to automatically identify and remediate vulnerabilities that attackers might exploit, creating a more proactive security posture.
6. Emphasis on User Experience (UX) for Security Analysts:
Vendors will focus more on intuitive interfaces, streamlined workflows, and enhanced visualization tools to improve the efficiency and effectiveness of security analysts, especially in the face of the cybersecurity talent shortage.
These trends highlight a future where EDR is not just about endpoint protection but is a critical component of an integrated, intelligent, and automated security ecosystem.
Implementing and Optimizing Your EDR Solution
Once you’ve completed your EDR Solutions Comparison and chosen a platform, successful implementation and ongoing optimization are crucial for maximizing its effectiveness.
1. Strategic Deployment:
- Phased Rollout: Begin with a pilot program on a small, representative group of endpoints before a full-scale deployment to identify and resolve any issues.
- Agent Installation: Ensure smooth and consistent agent deployment across all relevant endpoints, including remote devices and cloud workloads.
2. Configuration and Tuning:
- Policy Customization: Tailor detection and response policies to your organization’s specific risk profile, industry, and compliance requirements.
- False Positive Reduction: Continuously monitor and tune the EDR solution to minimize false positives, which can lead to alert fatigue and divert security resources.
3. Integration with Existing Security Tools:
- SIEM/SOAR Integration: Integrate EDR data with your SIEM for centralized logging and correlation, and with SOAR for automated incident response workflows.
- Threat Intelligence Feeds: Ensure the EDR solution is consuming relevant threat intelligence to enhance its detection capabilities.
4. Regular Monitoring and Threat Hunting:
- Active Monitoring: Establish processes for continuous monitoring of EDR alerts and dashboards.
- Proactive Threat Hunting: Empower your security team (or MDR provider) to conduct regular threat hunts, leveraging the EDR’s visibility and forensic capabilities.
5. Training and Awareness:
- Security Team Training: Provide comprehensive training to your security operations team on how to effectively use and manage the EDR platform.
- User Awareness: Educate end-users on security best practices to reduce the likelihood of successful attacks.
6. Regular Review and Updates:
- Performance Review: Periodically review the EDR solution’s performance, detection rates, and response times.
- Software Updates: Keep the EDR agent and management console updated to benefit from the latest features, threat intelligence, and security patches.

Conclusion: Securing Your Future with the Right EDR Solution
The year 2026 presents both unprecedented opportunities and intensified cyber threats for U.S. businesses. In this dynamic environment, a robust EDR solution is not merely a defensive tool but a strategic asset that enables resilience, ensures business continuity, and protects sensitive data. Our comprehensive EDR Solutions Comparison has provided a framework for understanding the critical aspects of EDR and evaluating leading vendors.
The journey to selecting and implementing the right EDR platform is multifaceted. It requires a deep understanding of your organization’s unique security posture, a clear vision of your threat landscape, and a commitment to ongoing optimization. By carefully considering detection capabilities, response mechanisms, visibility, performance, ease of use, support, and cost, U.S. businesses can make an informed decision that significantly strengthens their cybersecurity defenses.
Remember that the best EDR solution is one that fits seamlessly into your existing security ecosystem, scales with your business needs, and empowers your security team (or managed service provider) to effectively detect, investigate, and respond to the most sophisticated cyber threats. As you move forward, leverage the insights from this EDR Solutions Comparison to secure your endpoints and safeguard your business in the digital future.





