Incident Response Planning: Build a Robust US Plan in 30 Days

Anúncios
Developing a comprehensive incident response plan within 30 days is essential for US organizations to effectively detect, contain, and recover from cyber threats, safeguarding critical assets and maintaining operational resilience.
Anúncios
In today’s interconnected landscape, the question isn’t if your organization will face a cyber incident, but when. For US organizations, a robust incident response planning framework is not just good practice; it’s a critical imperative for survival and trust. This guide will walk you through building an effective plan in less than 30 days, ensuring your business is prepared for the inevitable.
Anúncios
Understanding the Urgency of Incident Response Planning
The digital threat landscape is constantly evolving, with new vulnerabilities and sophisticated attack vectors emerging daily. For US organizations, the stakes are particularly high, given stringent data privacy regulations and the potential for significant financial and reputational damage. Proactive incident response planning is the cornerstone of a resilient cybersecurity posture.
Without a clear and tested plan, a cyber incident can quickly spiral into a crisis, leading to prolonged downtime, data loss, regulatory fines, and erosion of customer confidence. The ability to respond swiftly and effectively directly impacts the severity and duration of an attack’s impact. This urgency is what drives the need to develop a comprehensive plan within a concise timeframe.
The cost of inaction
Delaying the development of an incident response plan can result in substantial consequences. Organizations without a plan often face higher costs per incident, longer recovery times, and increased legal liabilities. The financial repercussions can include:
- Direct costs: Ransom payments, forensic investigations, legal fees, credit monitoring services.
- Indirect costs: Lost revenue due to downtime, reputational damage, customer churn.
- Regulatory fines: Penalties for non-compliance with regulations like GDPR, CCPA, or HIPAA.
Beyond financial implications, the damage to an organization’s brand and customer trust can be irreversible. Therefore, prioritizing incident response planning is an investment in your organization’s future and stability.
The imperative to establish a solid incident response plan within a month stems from the rapid pace of cyber threats and the severe consequences of being unprepared. A well-defined plan enables a systematic approach to handling security breaches, minimizing disruption, and protecting vital assets.
Phase 1: Foundation and Team Building (Days 1-7)
The initial phase of building your incident response plan focuses on laying the groundwork and assembling the right team. This is where you establish the core structure and define roles, ensuring everyone understands their responsibilities when an incident occurs. This foundational work is crucial for the subsequent rapid development of the plan.
Effective incident response is a team sport, requiring collaboration across various departments. Identifying key stakeholders and defining their roles and responsibilities early on will streamline the entire process.
Assembling your incident response team
Your incident response team should be multidisciplinary, drawing expertise from IT, legal, public relations, human resources, and senior management. Each role brings a unique perspective and essential skills to the table.
- Core IT/Security Team: Responsible for technical detection, containment, and eradication.
- Legal Counsel: Guides on regulatory compliance, data breach notification laws, and potential litigation.
- Public Relations/Communications: Manages external and internal communications to protect the organization’s reputation.
- Human Resources: Addresses employee-related issues, such as insider threats or personnel involvement in incidents.
- Senior Management: Provides strategic guidance, approves resources, and makes high-level decisions.
Clearly defining who does what, when, and how is paramount. This includes establishing a clear chain of command and communication protocols within the team and with external parties.
During this first week, focus on identifying critical assets, understanding your organization’s risk profile, and securing executive buy-in. These elements provide the necessary context and support for developing a truly effective incident response plan. Without this strong foundation, subsequent steps will be less effective.
Phase 2: Developing the Core Plan (Days 8-14)
With the team assembled and foundational knowledge in place, the second week is dedicated to drafting the core components of your incident response plan. This involves outlining the procedures and protocols that will guide your organization through an incident, from initial detection to full recovery. This phase transforms theoretical understanding into actionable steps.
A well-structured plan follows a systematic approach, ensuring that no critical step is overlooked during the chaos of an actual incident. The key is to standardize processes as much as possible to enable consistent and efficient responses.
Key elements of the incident response plan
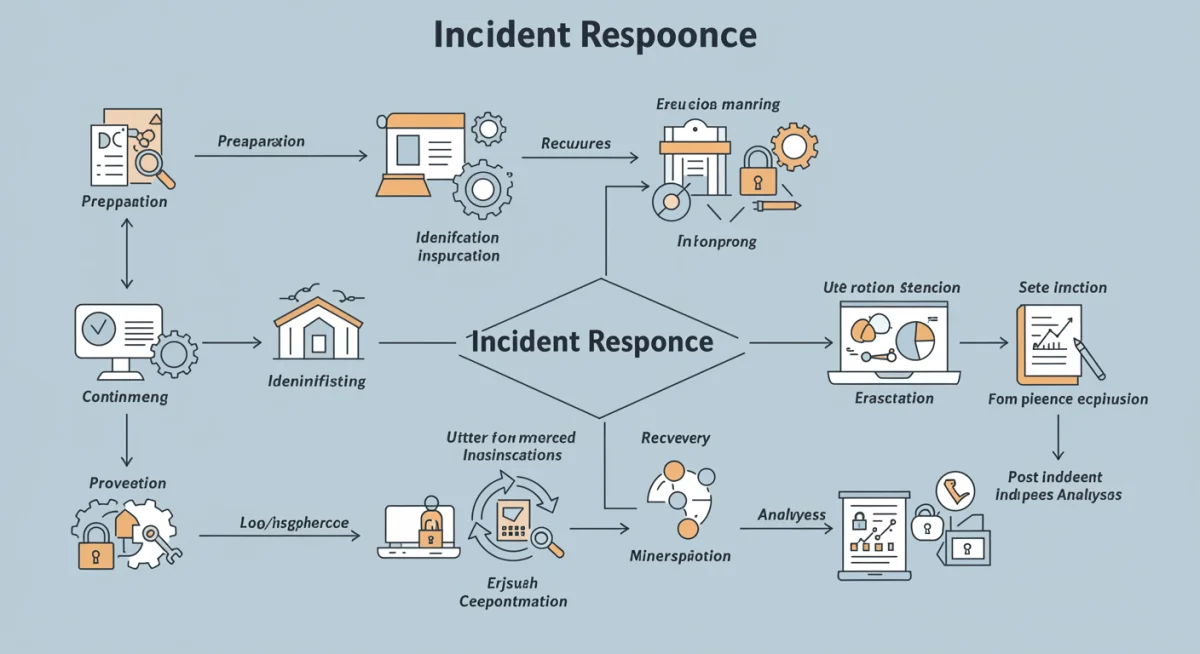
The plan should clearly delineate the steps for each phase of the incident response lifecycle. This includes:
- Preparation: Beyond team building, this involves defining policies, acquiring necessary tools, and conducting training.
- Identification: How incidents are detected, analyzed, and prioritized. This includes defining what constitutes an incident and establishing reporting mechanisms.
- Containment: Strategies to limit the scope and impact of an incident, such as isolating affected systems or shutting down compromised services.
- Eradication: Removing the cause of the incident, whether it’s malware, vulnerabilities, or unauthorized access.
- Recovery: Restoring affected systems and data to normal operation, including testing and validation.
- Post-Incident Analysis: Learning from the incident, documenting findings, and implementing improvements.
Each of these phases requires detailed procedures, checklists, and decision trees to guide the incident response team. Consider various incident types—malware, phishing, data breaches, denial-of-service attacks—and tailor responses accordingly. This level of detail ensures comprehensive coverage.
This week’s objective is to produce a first draft of the incident response plan, including detailed workflows and communication matrices. While it won’t be perfect, having a tangible document allows for review and refinement in the subsequent stages, moving your organization closer to a complete incident response planning capability.
Phase 3: Communication and Legal Frameworks (Days 15-21)
The third week shifts focus to critical external and internal communication strategies, alongside ensuring legal and regulatory compliance. An incident response plan is incomplete without a robust communication strategy that addresses all stakeholders, from employees to customers and regulatory bodies. This phase also ensures your plan aligns with US specific legal requirements, minimizing potential liabilities.
Clear, consistent, and timely communication can significantly mitigate the reputational damage and legal risks associated with a cyber incident. Understanding the legal landscape is equally important for US organizations, as various federal and state laws dictate breach notification requirements.
Crafting communication strategies
Develop pre-approved communication templates for different scenarios. These templates should cover:
- Internal Communications: How and when to inform employees, ensuring they know their roles and responsibilities during an incident.
- Customer Communications: Draft messages for affected customers, explaining the situation, steps being taken, and offering support where appropriate. Transparency is key.
- Media Relations: Prepare statements for the press, designating a single point of contact to avoid conflicting information.
- Regulatory Notifications: Understand and outline the specific requirements for notifying relevant authorities, such as state attorneys general or federal agencies, depending on the nature of the breach.
Practice these communication flows during drills to ensure seamless execution when an actual incident occurs. The legal counsel on your incident response team will be instrumental in reviewing these communications.
Simultaneously, dedicate time to reviewing federal and state-specific data breach notification laws applicable to your organization. This includes understanding reporting timelines, content requirements for notifications, and potential penalties for non-compliance. Ensuring your incident response planning incorporates these legal requirements from the outset is crucial for minimizing legal exposure.
Phase 4: Testing, Training, and Refinement (Days 22-28)
The penultimate week is dedicated to validating your incident response plan through testing, training your team, and refining the document based on feedback. A plan, no matter how well-written, is only as good as its execution. This phase ensures that your team is prepared to act swiftly and effectively when a real incident strikes, transforming theoretical knowledge into practical capability.
Regular testing and training are vital for identifying gaps in the plan and ensuring that all team members are confident in their roles and responsibilities. This iterative process of review and improvement strengthens the overall resilience of your organization.
Conducting drills and exercises
Organize tabletop exercises or simulation drills to test the plan in a controlled environment. These exercises can range from discussing hypothetical scenarios to full-scale simulations involving mock attacks. Key objectives include:
- Assessing the team’s understanding of roles and responsibilities.
- Identifying weaknesses in communication flows and decision-making processes.
- Evaluating the effectiveness of containment and recovery procedures.
- Testing the functionality of technical tools and resources.
Document all observations and lessons learned from these drills. This feedback is invaluable for refining the plan.
Concurrently, conduct training sessions for all relevant personnel, not just the core incident response team. This includes general cybersecurity awareness training for all employees, as they are often the first line of defense. Ensure that everyone understands how to identify and report suspicious activities.
Based on the insights gained from testing and training, revise and update your incident response plan. This could involve clarifying procedures, adding new sections, or adjusting communication strategies. The goal is to create a dynamic document that evolves with your organization’s needs and the threat landscape, solidifying your incident response planning efforts.
Phase 5: Finalization and Continuous Improvement (Days 29-30)
In the final two days of your 30-day sprint, the focus is on formalizing the incident response plan and establishing a framework for continuous improvement. This ensures the plan remains relevant and effective over time, adapting to new threats and organizational changes. A static plan quickly becomes an outdated and ineffective plan.
Formal approval signifies organizational commitment and ensures that the plan is integrated into the broader security strategy. Continuous improvement mechanisms guarantee its long-term viability and effectiveness.
Formalizing the plan
Obtain official sign-off from senior management and legal counsel. This step is crucial for establishing the plan’s authority and ensuring it has the necessary resources and support. Once approved, disseminate the plan to all relevant stakeholders and ensure it is easily accessible.
Consider creating different versions or summaries of the plan tailored to specific audiences. For example, a high-level overview for executives and a detailed technical guide for the IT security team.
Establishing a continuous improvement cycle
Incident response planning is not a one-time project; it’s an ongoing process. Implement a schedule for regular reviews and updates:
- Annual Reviews: Conduct comprehensive reviews of the entire plan at least once a year, or whenever there are significant changes to the organization’s infrastructure, personnel, or risk profile.
- Post-Incident Reviews: After every actual incident, perform a thorough post-mortem analysis to identify areas for improvement in the plan and its execution.
- Threat Intelligence Integration: Continuously monitor the threat landscape and integrate new intelligence into your plan to anticipate and prepare for emerging threats.
By day 30, your US organization will have a robust, actionable incident response plan, ready to face the challenges of the modern cyber landscape. This systematic approach ensures that you are not just reacting to incidents but proactively managing and mitigating their impact through effective incident response planning.
| Key Aspect | Brief Description |
|---|---|
| Team Building | Assemble a multidisciplinary team with clear roles to manage incidents. |
| Plan Development | Draft detailed procedures for detection, containment, eradication, and recovery. |
| Communication & Legal | Establish communication protocols and ensure compliance with US data breach laws. |
| Testing & Training | Validate the plan through drills and train staff for effective execution. |
Frequently asked questions about incident response planning
Incident response planning is vital for US organizations due to escalating cyber threats and strict regulatory requirements like HIPAA, CCPA, and state breach notification laws. A robust plan minimizes financial losses, reputational damage, and legal penalties by enabling swift and effective handling of security breaches.
The key phases include preparation, identification, containment, eradication, recovery, and post-incident analysis. Each phase involves specific steps and protocols designed to systematically address a cyber incident, from initial detection to full operational restoration and learning from the event.
An effective incident response team should be multidisciplinary, typically including IT security specialists, legal counsel, public relations professionals, human resources representatives, and senior management. This diverse expertise ensures comprehensive handling of technical, legal, communication, and personnel aspects of an incident.
An incident response plan should be a living document, updated regularly. It’s recommended to conduct comprehensive reviews at least annually, or whenever there are significant changes in organizational infrastructure, personnel, or the threat landscape. Post-incident reviews are also crucial for continuous improvement.
Yes, even small US businesses can establish a functional incident response plan within 30 days by focusing on core components. Prioritize identifying critical assets, defining essential roles, and creating simplified procedures for detection, containment, and communication. Leverage templates and basic cybersecurity tools to accelerate the process.
Conclusion
Developing a robust incident response plan in less than 30 days is an ambitious yet achievable goal for any US organization. By systematically tackling team building, plan development, communication strategies, legal compliance, and rigorous testing, businesses can significantly enhance their digital security posture. The rapid evolution of cyber threats demands immediate and decisive action. Investing in comprehensive incident response planning is not merely a defensive measure; it’s a strategic imperative that safeguards your organization’s operational continuity, reputation, and financial health in an increasingly complex digital world.





